Directories
¶
Directories
¶
| Path | Synopsis |
|---|---|
|
libsubfinder
|
|
|
engines/passive
Passive Subdomain Discovery Helper method Calls all the functions and also manages error handling
|
Passive Subdomain Discovery Helper method Calls all the functions and also manages error handling |
|
output
Contains different functions for reporting
|
Contains different functions for reporting |
|
sources/censys
A golang client for Censys Subdomain Discovery
|
A golang client for Censys Subdomain Discovery |
|
sources/certdb
A CertDB Subdomain parser in golang
|
A CertDB Subdomain parser in golang |
|
sources/certspotter
A Golang based client for Certspotter Parsing
|
A Golang based client for Certspotter Parsing |
|
sources/crtsh
A Golang based client for CRT.SH Parsing
|
A Golang based client for CRT.SH Parsing |
|
sources/dnsdb
Golang driver from dnsdb.org
|
Golang driver from dnsdb.org |
|
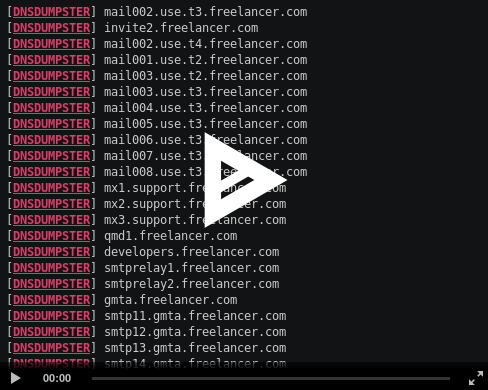
sources/dnsdumpster
A Parser for subdomains from DNSDumpster
|
A Parser for subdomains from DNSDumpster |
|
sources/findsubdomains
Golang driver from findsubdomains.com
|
Golang driver from findsubdomains.com |
|
sources/hackertarget
A golang based Hackertarget subdomains search client
|
A golang based Hackertarget subdomains search client |
|
sources/netcraft
Netcraft Scraping Engine in Golang
|
Netcraft Scraping Engine in Golang |
|
sources/passivetotal
A golang client for Passive total Subdomain Discovery
|
A golang client for Passive total Subdomain Discovery |
|
sources/ptrarchive
A PTRArchive subdomain parser in golang
|
A PTRArchive subdomain parser in golang |
|
sources/riddler
A Parser for subdomains from Riddler
|
A Parser for subdomains from Riddler |
|
sources/securitytrails
A golang SecurityTrails API client for subdomain discovery.
|
A golang SecurityTrails API client for subdomain discovery. |
|
sources/threatcrowd
A Golang based client for Threatcrowd API
|
A Golang based client for Threatcrowd API |
|
sources/threatminer
A ThreatMiner subdomain parser in golang
|
A ThreatMiner subdomain parser in golang |
|
sources/virustotal
A Virustotal Client for Subdomain Enumeration
|
A Virustotal Client for Subdomain Enumeration |
|
sources/waybackarchive
A Golang based client for Parsing Subdomains from Waybackarchive
|
A Golang based client for Parsing Subdomains from Waybackarchive |
Click to show internal directories.
Click to hide internal directories.